The Emergence of New Malware Variants
Recent developments have shown a surge in new malware variants, with WordPress websites serving as launch pads for malicious attacks. These sites are being exploited to trick visitors into executing harmful PowerShell commands on their Windows machines, leading to the installation of the LummaStealer trojan malware.
What is LummaStealer?
LummaStealer, also referred to as LummaC2, is a malicious software designed to clandestinely gather sensitive data. This can include login credentials, browser cookies, cryptocurrency wallet information, and other valuable personal or system details. It typically operates covertly to avoid detection for as long as possible.
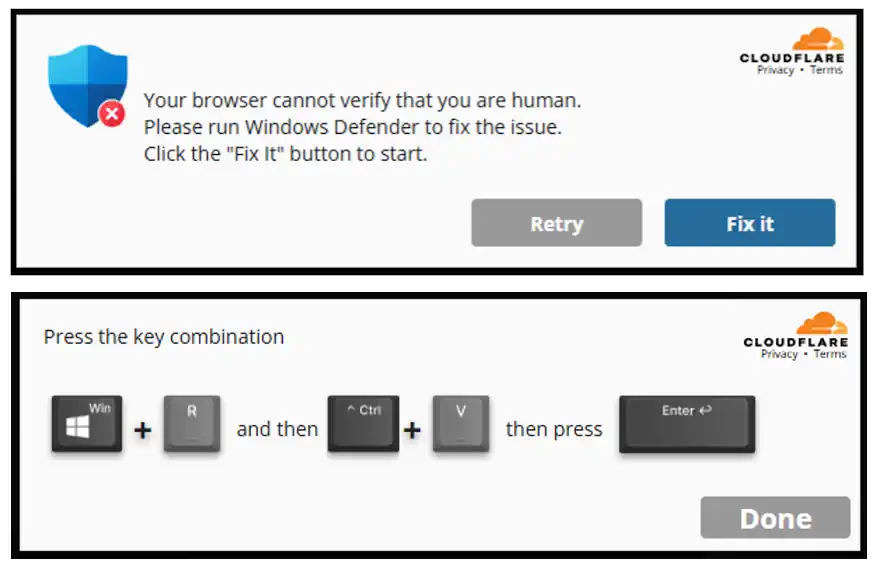
Malicious WordPress Plugins
Attackers have resorted to designing malicious WordPress plugins to trick users into installing this malware. These plugins are often masked as human verification tests. However, no user should ever need to run any PowerShell commands or “Run Windows Defender” to interact with a website.
Targeted Operating Systems
These fake human verification prompts only appear on computers using the Windows operating system, which is the malware’s primary target. Computers using Linux or Mac are unaffected and do not receive these prompts.
Backend Malware Operation
Several recently witnessed variants of the malware have been traced back to malicious plugins. These plugins use heavy hex encoding, which can be easily deobfuscated. The attackers have also been found to abuse legitimate URL shortening services to obfuscate the true destination and location of their malware payload.
The Extent of the Attack
Once the malware is deployed on the victim’s computer, the attackers gain full access to the system. They can intercept login information from banks or crypto wallets, social media passwords, login cookies, and any other data present on the system. LummaStealer tends to remain concealed for as long as possible to maximize its returns.
Admin User Generator: A Backdoor Entry
The malicious plugin also features an admin user generator that acts as a backdoor into the WordPress environment. It hides the generated admin user from view and also conceals itself from the list of installed plugins on the infected WordPress website.
Precautionary Measures for Web Users
Web users should be cautious of such malware infections and avoid running any strange commands on their computers. It’s important to notify the website owner if this infection displays itself on your screen. Also, it’s advisable to enable 2FA on your logins to prevent attackers from accessing your bank or social media accounts in the event of a malware attack.
For Website Owners
If your website falls victim to this malware, professional assistance can help remove the infection and secure your site. Regular monitoring and updating of your website’s security measures can prevent such attacks.